5 Steps to Master Character AI Age Verification Risk (March 2026)
- Map your endpoint network exposure to consumer AI chatbot platforms.
- Deploy Zero Trust identity verification APIs across all LLM access gateways.
- Migrate high-risk employee workflows to sovereign, enterprise-grade AI platforms.
- Implement local LLM hardware hosting for secure, unfiltered developer access.
- Automate continuous compliance tracking for COPPA and GDPR-K mandates.
Unregulated consumer AI chatbots are silently infiltrating your corporate network, exposing your enterprise to massive data leaks and compliance violations.
While employees actively search for ways to bypass age gates and safety filters on platforms like Character AI, traditional firewalls are failing to stop this new wave of Shadow AI. To secure your perimeter, you must master the Character AI age verification process and establish internal governance.
This comprehensive guide provides a 5-step framework to master AI age verification risks, secure your digital perimeter, and transition to compliant, enterprise-grade models.
What Most Organizations Miss About Shadow AI Identity Fraud
The most dangerous assumption IT leaders make today is believing that standard web filters can stop employees from interacting with consumer AI. The reality is far more complex.
Modern generative AI platforms utilize dynamic IPs, API tunneling, and mobile application ecosystems that easily bypass legacy Secure Web Gateways (SWG). When employees want to use AI tools for brainstorming, coding, or drafting emails, they will find a way.
If those tools require age verification or identity checks, users often resort to using personal credentials, fake birthdays, or unauthorized VPNs. This behavior creates a catastrophic security blind spot. You are no longer just dealing with lost productivity; you are dealing with identity spoofing and unauthorized data exfiltration on your corporate network.
Identity spoofing against AI systems is rapidly becoming the dangerous new frontier of corporate fraud. As detailed in Why Tricking Character AI Age Verification Fails, modern AI platforms are actively deploying biometric verification APIs, Liveness Detection, and strict KYC compliance checks to flag and block synthetic identities.
If an employee uses a corporate device to engage in identity fraud just to bypass an AI age gate, the legal liability often falls back on the enterprise. To mitigate this, organizations must shift their perspective. You cannot merely block the AI; you must architect a secure, verifiable pathway for employees to access the artificial intelligence tools they need without violating global privacy laws.
Step 1: Audit and Map Your Current AI Exposure
The first step to mastering Character AI age verification risk is achieving absolute visibility into your current network traffic. You cannot secure what you cannot see.
Begin by running a comprehensive Shadow IT audit specifically tuned for generative AI endpoints. Traditional network monitoring tools may group AI chatbot traffic under general "web browsing" or "cloud services."
You must configure your Cloud Access Security Broker (CASB) to explicitly flag traffic directed toward consumer LLMs, unauthorized API calls, and known age-gated AI platforms. Once you have visibility, you will likely discover a high volume of unauthorized access attempts.
When employees attempt workarounds to access these systems, the security consequences escalate rapidly. In fact, understanding Why Bypassing Character AI Age Restrictions is Fatal is the first step in recognizing how these consumer-level hacks introduce severe malware, phishing vulnerabilities, and privacy risks directly into your corporate ecosystem.
After mapping the exposure, IT leaders must categorize the risk based on the data being shared. Are employees using these tools for benign tasks like writing generic marketing copy, or are they pasting sensitive customer data into consumer chatbots that lack enterprise data protection agreements?
Step 2: Implement Zero Trust Identity Verification APIs
Once you have mapped your exposure, you must overhaul your access architecture. Relying on simple password authentication or basic web filtering is insufficient for the AI era.
Enterprises must adopt a Zero Trust Architecture (ZTA) that explicitly verifies the identity and context of every user attempting to access an AI tool. Zero Trust means shifting the verification burden away from the consumer AI platform and bringing it inside your corporate perimeter.
Before an employee can send a prompt to any LLM, their identity, device posture, and network location must be continuously authenticated. Implement robust identity verification APIs that support Multi-Factor Authentication (MFA) and biometric Liveness Detection.
This ensures that the person accessing the AI is exactly who they claim to be, eliminating the risk of employees using fake credentials or shared accounts to bypass age restrictions. Furthermore, these identity APIs should be tied directly to your role-based access control (RBAC) systems.
An intern should not have the same level of AI access as a senior data scientist. By granularly controlling who can access which AI models, you drastically reduce the risk of compliance violations and unauthorized data sharing.
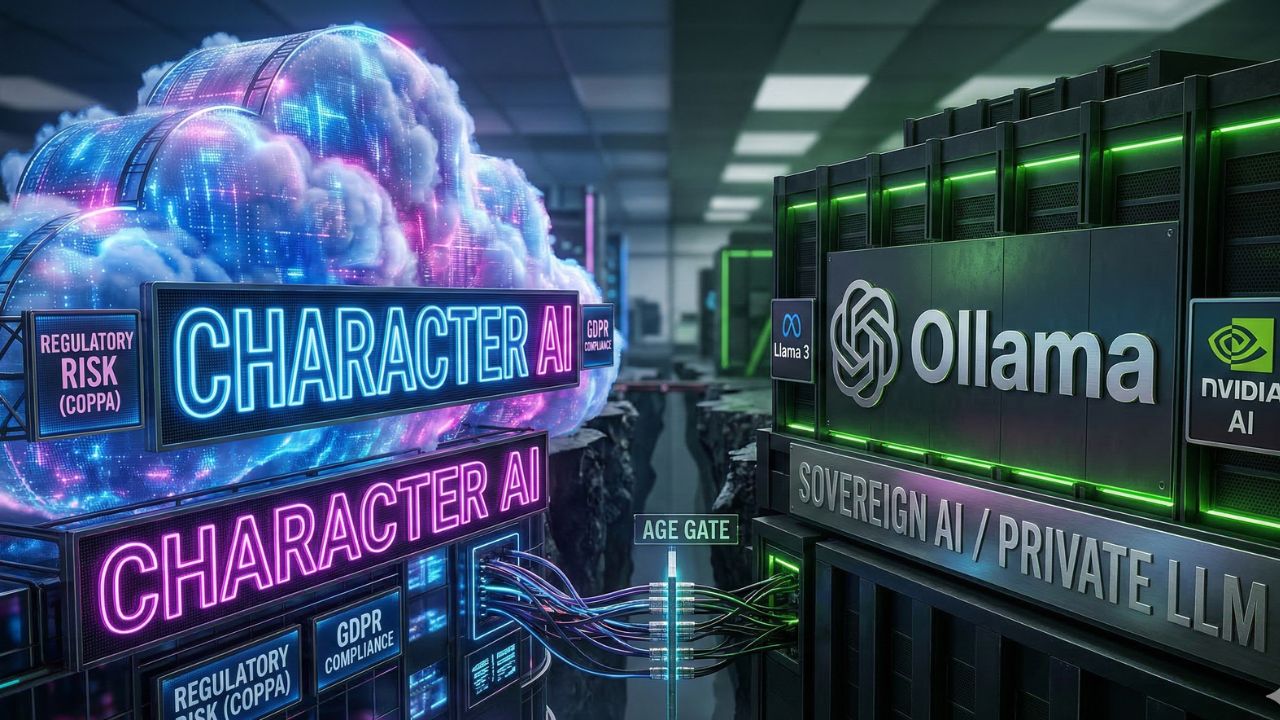
Step 3: Deploy Enterprise-Grade Sovereign AI Models
The most effective way to eliminate the risks associated with consumer AI age verification is to completely remove the need for consumer AI in the workplace.
If your employees are desperate to use AI, you must provide them with a secure, sanctioned alternative that is governed by your internal IT policies. This means transitioning away from public, age-gated chatbots and investing in Enterprise-Grade Sovereign AI models.
Sovereign AI refers to platforms where you maintain absolute control over the data, the infrastructure, and the underlying model weights. Many executives are unaware that relying on consumer-level bypasses violates core compliance standards.
Exploring The C.AI Age Verification Bypass Truth NIST Hides reveals why forward-thinking organizations are abandoning consumer AI chatbots in favor of secure, unfiltered enterprise AI platforms.
When you deploy a sovereign AI model, you eliminate the "black box" risk. Your corporate data is no longer being used to train a public LLM, and your employees are no longer subjected to arbitrary, third-party age verification gates.
You control the access, you control the safety guardrails, and you own the resulting intellectual property. This shift transforms AI from a massive security liability into a proprietary business asset.
Step 4: Host Local LLMs for Unrestricted, Compliant Access
While cloud-based enterprise AI is excellent for general knowledge workers, your software engineers and data scientists often require a different class of tools.
Developers frequently need to push the boundaries of AI, requiring unfiltered models for advanced coding, debugging, and penetration testing without cloud-imposed latency or arbitrary content constraints. The solution is moving the compute power on-premise.
By implementing 3 Ways to Run AI Without Age Verification Limits, your engineering teams can leverage secure, private local LLMs without relying on restrictive, consumer-facing cloud servers.
Hosting open-source models like Llama 3 or Mistral locally on dedicated GPU hardware or advanced AI PCs completely bypasses the need for external age verification. Because the model runs entirely within your air-gapped network or localized hardware, there is zero risk of data exfiltration to a third-party server.
This approach gives your high-performance teams the absolute freedom to innovate while maintaining strict compliance with enterprise data privacy standards. It is the ultimate balance between unrestricted AI capabilities and ironclad corporate security.
Step 5: Automate Compliance for COPPA and GDPR-K
The final step in mastering AI age verification risk is fortifying your legal and regulatory compliance. The global regulatory landscape regarding artificial intelligence, data privacy, and the protection of minors is evolving at breakneck speed.
If your enterprise operates globally, or if your digital products interact with younger demographics, you must be acutely aware of regulations like the Children's Online Privacy Protection Act (COPPA) in the US and the GDPR-K (the children’s specific provisions of the General Data Protection Regulation) in Europe.
Consumer AI platforms enforce age verification precisely to avoid the devastating fines associated with violating these laws. If your employees bypass these gates using corporate networks, your company could be found complicit in circumventing federal privacy regulations.
To manage this, CISOs must automate continuous compliance tracking. Deploy AI governance software that automatically logs all LLM interactions, audits user identity protocols, and flags any potential violation of COPPA or GDPR-K standards.
Your legal team must work in tandem with IT to ensure that your internal AI usage policies explicitly forbid the use of unauthorized consumer chatbots. By automating your audit trails and enforcing strict data retention policies for all sanctioned AI interactions, you build an impenetrable legal shield around your organization.
The Future of AI Safety Guardrails
The arms race between generative AI capabilities and cybersecurity guardrails is only just beginning. As AI models become more autonomous and capable of executing complex workflows, the concept of basic "age verification" will evolve into comprehensive "identity and intent verification."
Furthermore, understanding compliance risks requires product owners to have a clear grasp of the underlying generative AI model types powering these conversational agents in order to properly evaluate their exposure.
As regulatory pressures and AI transformations disrupt the industry—evidenced by the recent Atlassian AI structural changes—leaders must adapt their governance frameworks to protect both their data and their workforce.
Organizations that attempt to block AI entirely will lose their competitive edge, suffering from reduced velocity and frustrated talent. Conversely, organizations that allow unregulated Shadow AI will inevitably suffer catastrophic data breaches.
The leaders who win the next decade will be those who master the middle ground. By auditing exposure, enforcing Zero Trust identity protocols, deploying sovereign models, and automating compliance, you can harness the full power of artificial intelligence while completely neutralizing the associated corporate risks.
Do not wait for a regulatory audit or a public data leak to take action. Secure your AI infrastructure today, and transform your digital workforce into a compliant, high-velocity engine of innovation.
Frequently Asked Questions (FAQ)
Character AI requires users to verify their age to ensure compliance with global privacy laws like COPPA and GDPR-K. This process restricts minors from accessing mature content and prevents the platform from illegally collecting data from underage users without parental consent.
Age verification acts as a primary security perimeter. By strictly controlling who accesses consumer AI platforms, these gates help prevent unauthorized users from interacting with the models, thereby reducing the likelihood of accidental corporate data leaks and identity spoofing.
Under COPPA, generative AI platforms cannot legally collect, store, or process personal information from children under 13 without verifiable parental consent. Failing to implement strict age verification mechanisms can result in millions of dollars in federal regulatory fines.
Using consumer platforms like Character AI on corporate networks is highly discouraged. It introduces severe Shadow AI risks, bypasses enterprise data protection agreements, and creates massive vulnerabilities for data exfiltration and compliance violations.
Identity verification APIs use advanced techniques like biometric Liveness Detection, document scanning, and database cross-referencing to confirm a user's true identity in real-time. This ensures that users cannot bypass safety protocols using fake credentials or VPNs.
Unfiltered LLMs lack essential safety guardrails, increasing the risk of generating biased, toxic, or legally compromising content. Furthermore, inputting proprietary corporate data into these public models often violates enterprise non-disclosure agreements and data privacy laws.
The best alternatives are secure, sovereign AI platforms and local LLMs. Hosting open-source models like Llama 3 or Mistral on dedicated corporate hardware provides teams with powerful, unrestricted AI capabilities while keeping all proprietary data strictly within the enterprise firewall.
