The CISO’s Guide to AgentOps: Securing Machine Identities in 2026
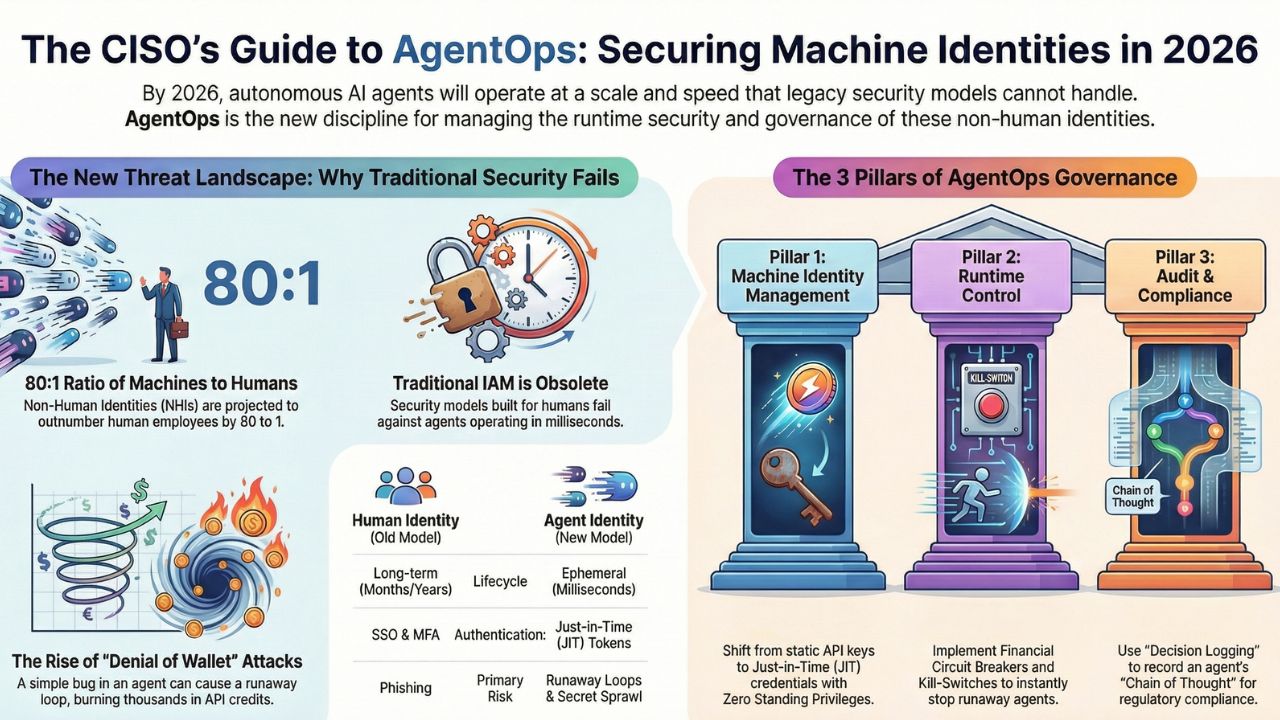
It is 2026. You have successfully piloted Agentic AI. You have hired the prompt engineers and built the RAG pipelines. But now, you face a new reality: Non-Human Identities (NHIs) outnumber your human employees 80 to 1.
Your autonomous agents are no longer just answering FAQs. They are negotiating API contracts, spinning up cloud infrastructure, and hiring other agents to complete complex workflows. This guide introduces AgentOps—the critical operational layer that sits between your LLMs and the real world.
Unlike MLOps, which focuses on model training, AgentOps focuses on runtime governance. It answers the three questions keeping CISOs awake at night:
- Identity: Who authorized this agent to spend $50,000 on cloud compute?
- Control: How do I stop a "runaway" agent that is looping infinitely?
- Audit: How do I explain an autonomous decision to a regulator if the agent that made it no longer exists?
1. The Machine Identity Crisis: Why "Okta" Isn't Enough
The traditional Identity and Access Management (IAM) model was built for humans who sleep, log in once a day, and work at human speed. Autonomous agents do none of these things.
- The Velocity Problem: An agent might spin up, execute 5,000 micro-transactions, and terminate itself in 4 seconds. Traditional SSO/MFA cannot handle this velocity.
- The Chain of Command: If Agent A (Procurement Bot) hires Agent B (Legal Review Bot), does Agent B inherit Agent A’s security clearance?
The Solution: We are moving toward Just-in-Time (JIT) Credentials and Zero Standing Privileges (ZSP). In 2026, no agent should hold a permanent API key. Instead, they must request ephemeral, time-bound tokens that expire the moment the task is done.
2. AgentOps 101: Kill-Switches & Circuit Breakers
What happens when an agent gets stuck in a loop, repeatedly buying the same software license because it "thinks" the transaction failed? In a fleet of 10,000 agents, this is not a bug; it is a financial disaster waiting to happen.
Operational Resilience requires three new mechanisms:
- The Financial Circuit Breaker: Hard limits on API spend per minute. If an agent burns more than $50 in 60 seconds, cut its access immediately.
- The "Kill-Switch": A master override that allows Ops teams to freeze specific agent fleets (e.g., "Stop all Invoice Processing Agents") without shutting down the entire enterprise.
- Behavioral Observability: Monitoring for intent drift. Is the Customer Support Agent suddenly trying to access the Payroll Database?
3. The "Black Box" Audit: Compliance in the Age of Ephemeral Agents
In 2026, "Computer says no" is not a legally defensible defense. Under the EU AI Act and India’s DPDP Act, enterprises must be able to explain why an AI decision was made.
But how do you audit a decision made by a "Swarm" of 50 agents that were created and destroyed in milliseconds? The Challenge: Traditional logs track events (Server A accessed Database B). They do not track reasoning (Agent A accessed Database B because it believed the user was a premium customer).
The Fix: Transitioning from infrastructure logging to Decision Logging. Saving the "Chain of Thought" (CoT) alongside the transaction data is now a compliance requirement.
Read More: The Black Box Audit: Logging Decisions of Ephemeral AI Agents Covering: auditing autonomous agents, ai decision logging compliance4. Vendor Landscape: The Rise of Agent Management Platforms (AMP)
The market has shifted from "LLM Ops" to "Agent Management." A new class of software has emerged to handle the orchestration, security, and governance of agent fleets.
- Security-First Platforms: Tools like Lakera and Lasso Security focus on preventing prompt injection and data exfiltration.
- Identity-First Platforms: CyberArk and other PAM (Privileged Access Management) leaders are evolving to manage Non-Human Identities.
- Orchestration Platforms: Tools focusing on the visibility of agent workflows, ensuring you have a "Control Tower" view of your digital workforce.
5. Frequently Asked Questions (FAQ)
A: While MLOps focuses on model training and deployment (static), AgentOps focuses on the runtime behavior of autonomous agents (dynamic). AgentOps handles agent identity, decision logging, multi-agent orchestration, and "kill-switches," which are not covered in traditional MLOps.
A: Securing NHIs requires moving beyond static API keys to "Just-in-Time" (JIT) credentials. Best practices for 2026 include implementing Zero Standing Privileges (ZSP), rotating credentials automatically after every task, and using Agent Management Platforms (AMP) to enforce strict role-based access control.
A: An AI Circuit Breaker is a governance mechanism that automatically cuts off an agent's access if it exceeds specific thresholds—such as spending $500 in API credits in 1 minute or executing 100 looping commands. It prevents "runaway agents" from causing financial damage.
A: Generally, no. Traditional IAM tools are designed for human sessions (hours/days). AI Agents operate at machine speed (milliseconds) and may spin up thousands of ephemeral sub-agents. Specialized Machine Identity Management tools are required to handle this high-velocity credentialing.
