IAM for AI Agents: Why Your Okta Strategy Fails for Autonomous Bots

It is 2026. Your organization has successfully deployed autonomous agents. But while your workforce has evolved, your Identity and Access Management (IAM) strategy is stuck in 2020.
The traditional IAM model was built for humans who sleep, log in once a day, and work at human speed. Autonomous agents do none of these things. They operate at machine speed, creating a massive governance gap that legacy tools like Okta are struggling to close.
This guide explores the "Identity Crisis" of the Agentic Era and provides a roadmap for securing Non-Human Identities (NHI).
1. The Velocity Problem: Why SSO Breaks Down
Human identity management relies on stable sessions. You log in at 9:00 AM, authenticate via MFA, and stay logged in until 5:00 PM. This model collapses when applied to AI agents.
- Scale: An enterprise might have 5,000 employees but 500,000 ephemeral agents spinning up and down daily.
- Speed: An agent might execute 5,000 micro-transactions in 4 seconds. Traditional Single Sign-On (SSO) protocols cannot handle this volume of authentication requests without latency or failure.
- Context: If Agent A (Procurement Bot) hires Agent B (Legal Review Bot), Agent B needs instant access to specific files. Waiting for a human admin to approve a ticket is impossible.
2. The "Service Account" Trap
For years, developers have used "Service Accounts" as a bandage for machine identity. This is now a critical vulnerability.
Service accounts typically rely on static API keys or long-lived tokens. In a 2026 environment where agents are autonomous, this leads to "Secret Sprawl." If an agent is compromised, a static key gives attackers persistent access until someone manually revokes it. Research shows that 51% of organizations still do not have a formal process for revoking these long-lived secrets.
3. The Solution: JIT & Zero Standing Privileges
To secure the Autonomous Enterprise, we must move to Just-in-Time (JIT) Credentials.
In this model, no agent holds a permanent key. When an agent needs to access a database, it requests a token. The system verifies the agent's identity (using protocols like SPIFFE) and issues a token that is valid only for the duration of that specific task—sometimes just milliseconds.
This leads to Zero Standing Privileges (ZSP). ZSP ensures that when an agent is idle, it has zero access rights. This drastically reduces the attack surface, as there are no "always-on" admin accounts for attackers to target.
4. Comparison: Human Identity vs. Agent Identity
Understanding the fundamental differences is key to selecting the right tools.
| Feature | Human Identity (Traditional IAM) | Agent Identity (Machine IAM) |
|---|---|---|
| Primary User | Employees, Contractors, Partners | Bots, Microservices, AI Agents |
| Lifecycle | Long-term (Months/Years) | Ephemeral (Milliseconds to Minutes) |
| Authentication | SSO, MFA (Push, SMS, Biometric) | mTLS, API Keys, JIT Tokens |
| Volume | 1:1 (One ID per Human) | 1:N (Thousands of IDs per Task) |
| Risk Profile | Phishing, Weak Passwords | Secret Sprawl, Runaway Loops |
5. The Tooling Landscape: Beyond Okta
While Okta is evolving with new standards for agent security, specialized platforms are leading the charge in 2026.
Leaders like CyberArk and Delinea have shifted focus to "Machine Identity Security," offering tools that automate the rotation of secrets and enforce ZSP policies. Newer entrants are leveraging frameworks like SPIFFE to provide universal identity control planes for cloud-native agents.
Read More: Top 7 Agent Management Platforms (AMP) for 2026 Compare CyberArk, Lakera, and Lasso Security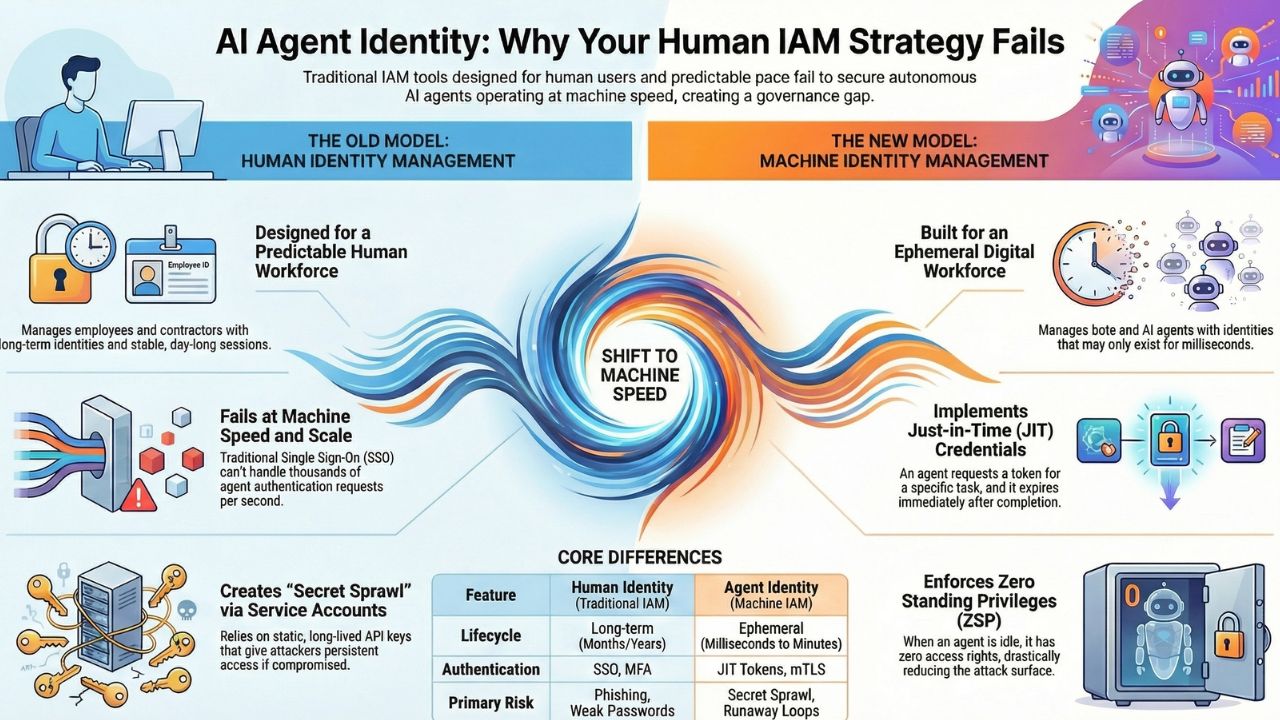
6. Frequently Asked Questions (FAQ)
A: Service accounts typically use static, long-lived credentials (API keys) that are often hard-coded and rarely rotated. AI agents require dynamic, short-lived tokens because they operate at high velocity and can be spun up or down in milliseconds, making static keys a major security risk.
A: JIT access for bots involves granting permissions only at the exact moment they are needed to perform a specific task. Once the task is complete, the access is immediately revoked, ensuring no "standing privileges" remain that attackers could exploit.
A: Human IAM is built for low-frequency, long-duration sessions (e.g., an 8-hour workday) using SSO and MFA. Machine IAM is built for high-frequency, short-duration interactions (e.g., milliseconds) requiring automated credential rotation and API-based verification.
7. Sources & References
- Cloud Security Alliance. "Agentic AI Identity Management Approach." Mar 2025.
- Okta. "From Code to Control: The Blueprint for Securing AI Agents at Enterprise Scale." Dec 2025.
- Okta. "AI Security: When Authorization Outlives Intent." Nov 2025.
- CyberArk. "AI agents and identity risks: How security will shift in 2026." Dec 2025.
- CrowdStrike. "What is Just-in-Time (JIT) Access?" Jan 2025.
- BeyondTrust. "Zero Standing Privileges (ZSP) Definition."
