The CareCloud Cyberattack: What IT Leaders Know So Far
Key Takeaways:
- A major supply chain wake-up call: The CareCloud breach exposes the fragile reality of healthcare SaaS and centralized electronic health records (EHR).
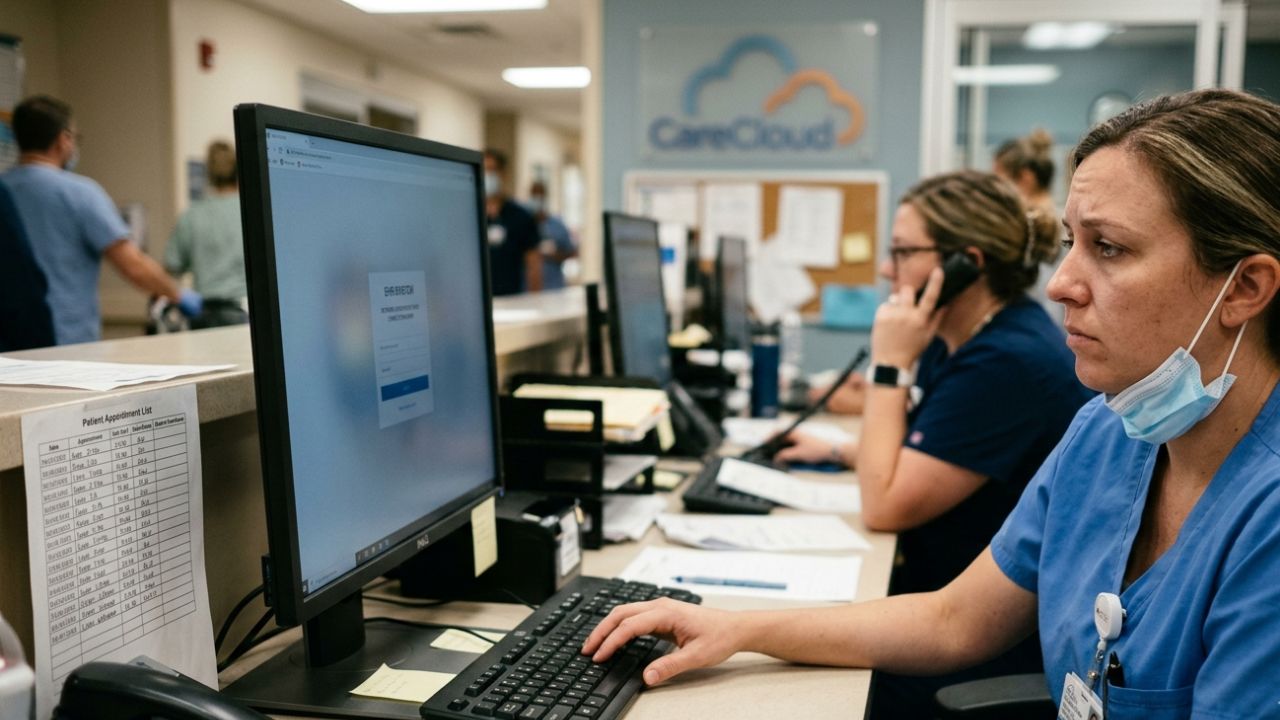
- Immediate disruption: On March 16, unauthorized actors breached CareCloud, a major healthcare IT provider, compromising one of its six EHR environments.
- Significant operational impact: The cyberattack caused an eight-hour network disruption and exposed sensitive patient medical records.
- Active response: A forensic investigation is currently active to determine the full scope of data exfiltration.
- Enterprise IT pivot: This incident requires teams to immediately implement zero-trust API architectures and self-healing fallback systems.
Introduction: The New Supply Chain Threat Landscape
The recent CareCloud cyberattack has fundamentally altered how enterprise IT leaders, Product Managers, and Agile engineering teams view third-party integrations. When a major cloud vendor experiences a structural security failure, the blast radius extends far beyond their internal infrastructure.
Our take cuts through the PR jargon to break down the immediate timeline and highlights why this is a massive supply chain wake-up call for enterprise IT and health-tech operations. Modern digital product development heavily relies on interconnected SaaS tools, and the trust placed in these systems is now being rigorously tested.
When those external dependencies are compromised, organizational resilience is tested to its absolute limits. This reality forces Chief Information Security Officers (CISOs) to adopt aggressive governance models. Mitigating these modern threats requires a unified strategy focused on securing enterprise infrastructure and machine identities across all distributed environments.
Relying on perimeter defense alone is an outdated paradigm. Today's connected enterprise must assume breach at the vendor level and architect systems designed to withstand third-party failures.
The CareCloud Intrusion Timeline
Every Agile software team fears the moment a trusted dependency unexpectedly collapses. A single compromised EHR environment brought CareCloud down for 8 hours. If your SaaS provider falls, your agile sprints won't save you—here is the exact timeline of the breach.
On March 16, unauthorized actors breached CareCloud, a major healthcare IT provider, compromising one of its six EHR environments. According to external reporting from InfoRiskToday reviewing the SEC filings, the company experienced a targeted network disruption that required immediate and drastic containment protocols.
The cyberattack caused an eight-hour network disruption and exposed sensitive patient medical records. During this eight-hour window, standard medical and administrative workflows stalled globally.
This disruption creates immense operational friction for the healthcare providers relying on these cloud services. From a Product Management perspective, eight hours of unscheduled downtime represents a catastrophic SLA breach. For AI leadership teams working on predictive health algorithms, losing access to this real-time data flow immediately breaks active models and invalidates sprint planning goals.
Which Specific EHR Environments Were Hit?
Enterprise architecture teams must understand exactly where the perimeter collapsed to prevent recurring incidents. Supply chain attacks like CareCloud force engineering teams to rethink third-party API trust.
The unauthorized actors compromised one of CareCloud's six EHR environments. This targeted infiltration highlights why implicit trust in external vendor systems is highly dangerous. Software architects and developers must pivot toward zero-trust integrations and self-healing fallback systems to protect core applications from external vendor vulnerabilities.
To prevent cascading failures during vendor breaches like the CareCloud attack, agile teams must implement zero-trust API architectures. Securing third-party API integrations requires automated circuit breakers, rigorous token auditing, and isolated staging environments to protect core workflows from external vulnerabilities.
You must secure these environments immediately. Industry analysts at eSecurity Planet note that incidents of this nature often originate from compromised credentials or unpatched vulnerabilities, stressing the need for granular access control. You wrote perfect code, but your vendor’s API just got breached. The CareCloud hack is a brutal reminder that trusting third-party integrations is an architectural failure.
Patient Data Exposure and Forensic Investigation Status
The most critical concern for any CTO or compliance officer is the integrity and privacy of protected health information (PHI). The cyberattack caused an eight-hour network disruption and exposed sensitive patient medical records.
A forensic investigation is currently active to determine the full scope of data exfiltration. While the technical forensics are being finalized, enterprise organizations must assume a worst-case scenario regarding their data assets.
The CareCloud breach isn't just an IT failure; it's a massive compliance and financial liability for CTOs and GCCs managing offshore health data. The CareCloud cyberattack exposes a massive liability gap for CTOs and Indian GCCs managing offshore medical records.
Relying on multi-tenant SaaS environments for sensitive health data invites severe compliance penalties under the DPDP Act and HIPAA, forcing a rapid pivot toward localized, sovereign infrastructure. We argue that sovereign infrastructure and rigorous vendor risk management are no longer optional for Indian leadership hubs trying to avoid DPDP Act and HIPAA penalties.
Your offshore healthcare GCC just became a massive legal liability. The CareCloud breach proves that relying on multi-tenant US SaaS providers is a compliance trap waiting to spring.
Why No Threat Group Has Claimed Ransomware (Yet)
In standard extortion events, threat actors loudly advertise their successful infiltrations to demand immediate payment. Interestingly, no prominent ransomware syndicate has publicly taken credit for this specific network disruption.
This silence is often highly strategic. Threat actors may be evaluating the quality and volume of the compromised data before launching a targeted extortion campaign. The absence of a ransomware note does not reduce the severity of the incident.
It simply indicates a potentially different, more calculated monetization strategy by the attackers, shifting the paradigm from immediate operational hostage-taking to prolonged data weaponization.
The Industry Shift to Quiet Data-Theft
Modern cybercrime is evolving rapidly into highly organized operations. We are witnessing an industry shift where attackers prioritize stealth over immediate operational disruption.
Quiet data-theft allows unauthorized actors to siphon sensitive information without triggering immediate automated alarms or alerting internal operations teams. This stolen data is subsequently sold on dark web marketplaces to other cybercriminals who specialize in identity theft or medical fraud.
For enterprise IT leaders, this shift requires advanced continuous monitoring. Simply waiting for a ransomware screen to appear is no longer a viable or acceptable security posture. Advanced threat detection must become a core component of daily IT operations.
Conclusion: Adapting to the Reality of Vendor Risk
The CareCloud cyberattack serves as an urgent catalyst for structural change in healthcare technology and enterprise architecture. IT leaders, CTOs, and Product Managers can no longer afford to treat SaaS vendor security as a secondary concern.
You must proactively audit your third-party integrations, implement zero-trust protocols across all endpoints, and shift toward sovereign infrastructure to protect your most critical data assets. Resilience is no longer optional; it is a foundational requirement for navigating the modern supply chain threat landscape.
FAQ: Understanding the Impact
The CareCloud outage was caused by a targeted cyberattack where unauthorized actors breached the network on March 16. The hackers successfully infiltrated one of the company's electronic health record (EHR) environments, triggering an immediate containment response that temporarily shut down network access.
The cyberattack successfully exposed sensitive patient medical records during the intrusion. However, a forensic investigation is currently active to determine the exact volume and full scope of the data exfiltration before finalizing reports on stolen files.
The security incident and subsequent response protocols resulted in significant operational downtime for healthcare providers. The cyberattack caused an eight-hour network disruption, temporarily halting critical medical services and workflows for users relying on the compromised EHR environment.
As of now, no threat group has officially claimed this as a ransomware attack. Instead, the incident aligns with an industry shift toward quiet data-theft, where attackers prioritize extracting sensitive records silently rather than immediately encrypting files for extortion.
Hackers target EHR systems by exploiting vulnerabilities in third-party API integrations, compromising service accounts, or utilizing stolen credentials. Relying on multi-tenant SaaS environments for sensitive health data provides a lucrative, centralized target for advanced cybercriminals seeking medical records.

